When the Threat Becomes Personal: A Red Teamer's Run-In with North Korea's IT Infiltration Scheme

Matt Mullins, offensive security researcher, recently sat down with Krittika Lalwaney, a fellow red teamer with deep social engineering expertise. One moment stood out: Krittika’s firsthand account of interviewing a North Korean threat actor.
A Scheme Bigger Than One Interview
According to multiple Wall Street Journal reports, North Korean spies have been systematically infiltrating US companies by posing as remote IT workers, interviewing for jobs – leveraging stolen identities, AI-generated headshots, and so-called “laptop farms” to mask their true location and keep income flowing back to North Korea. It’s a financially motivated, state-backed operation more companies are facing than we realize.
Krittika had read the WSJ piece. What she didn’t expect was to encounter it in her own hiring process.
The Interview
Krittika was hiring for an IT position when a resume landed in her pipeline that looked strong enough on paper. It had cleared screening (later she’d understand why: the resume had been carefully tuned with AI-optimized keywords designed to beat automated filters.) A recruiter call followed, handled smoothly by someone with confident enough English. Nothing alarming. The candidate moved forward.
Then came the video interview with Krittika.
The person who showed up wasn’t the same one who had taken the recruiter call. IP tracing later suggested that first call had come from Africa – pointing to a coordinated, multi-actor operation in which different “specialists” handle different stages of the hiring funnel. What arrived on Krittika’s screen was the technical leg of the operation.
And that’s where things started to unravel.
The Tells
As a social engineer, Krittika is professionally trained to notice what most people miss. Several things stood out immediately:
- The hat. Unusual in a professional interview setting, and almost certainly deliberate. It was a low-tech countermeasure against AI-based facial recognition tools that might flag or identify the individual.
- The background. A plain white wall that, in context, read less like a home office and more like a small dormitory – consistent with what the WSJ described as communal living arrangements for these workers.
- The resume recitation. When asked about experience, the candidate could only read back bullet points verbatim. Follow-up questions asking for real examples were met with silence or vague deflection because the experiences didn’t exist.
- The personal blanks. Krittika, a practiced social engineer, pivoted to casual conversation. The resume claimed a Columbia University background, so she asked about New York – Yankees games, neighborhoods, the kind of local texture anyone who’d actually lived there would know. Nothing landed. The candidate had no ability to think on their feet or improvise around gaps in their cover story.
Thirty minutes on the calendar became an impromptu research session. Krittika kept the conversation going, probing for what the operation could and couldn’t do.
What It Reveals About the Operation
The experience maps onto a broader pattern. North Korean operatives appear to function like any specialized team – each actor plays a defined role. Social engineering and native-language fluency get outsourced to other threat actor groups. The technical candidates focus on what they’re actually good at: the work. Once embedded, they produce genuine IT output, collect a salary, and route the money back through the network. IT farms maintain persistent VPN access to keep the illusion intact. That’s at least Krittika’s take.
Where This Is Heading
Krittika spotted the tells because she knew what to look for. But the tactics are evolving: AI-generated headshots, deepfaked video interviews, identity portfolios built at scale. The current generation of these operations has some blind spots when it comes to social tact and improvisation, but that won’t be true forever. As the tradecraft matures, the window for catching these actors on human instinct alone will narrow.
One Step Further
It’s worth thinking about the ‘what ifs.’ What if your business found itself unknowingly hiring a nation-state threat actor who produces enough work to keep their job? Then what? How do you protect against insider threat movements within your environment?
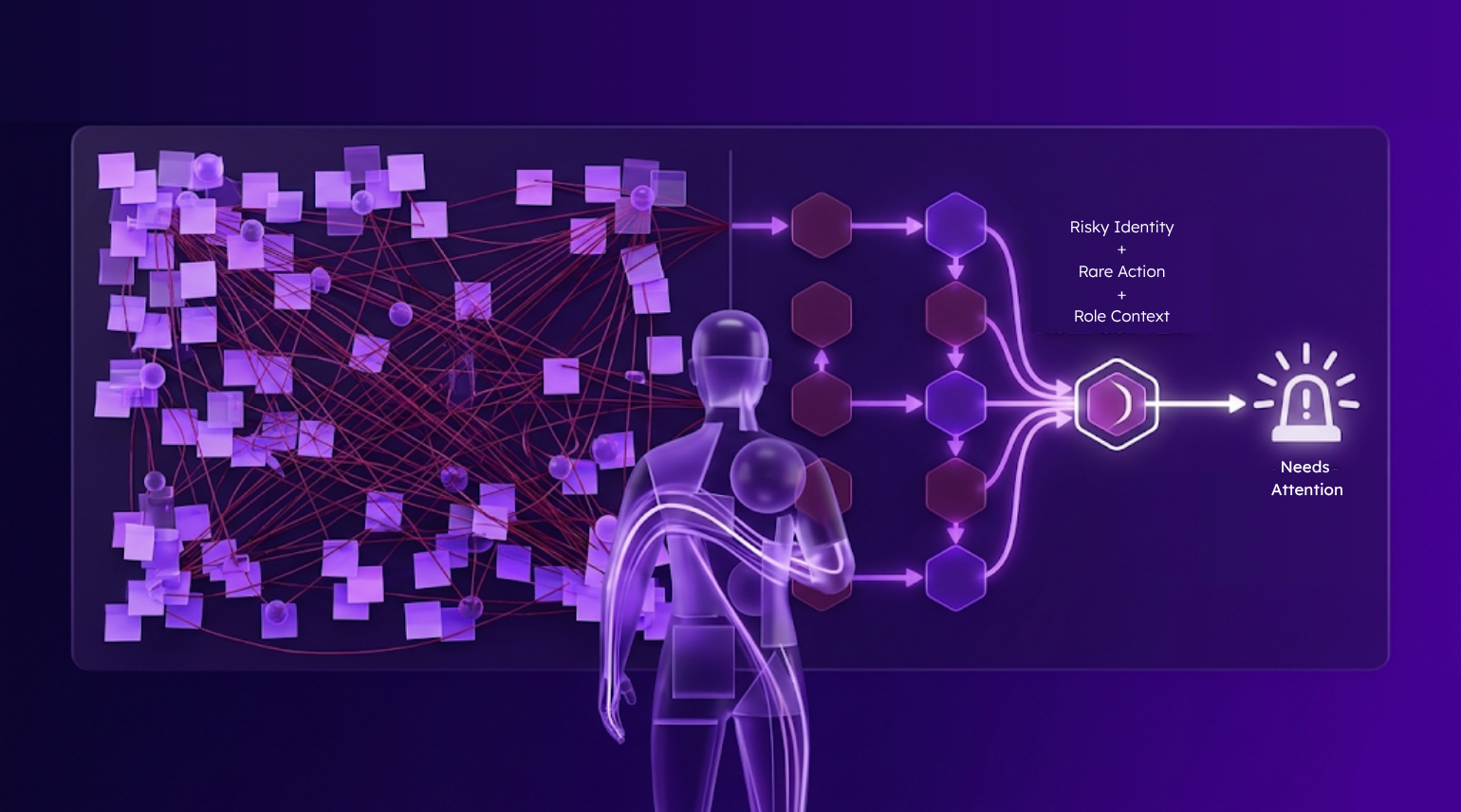
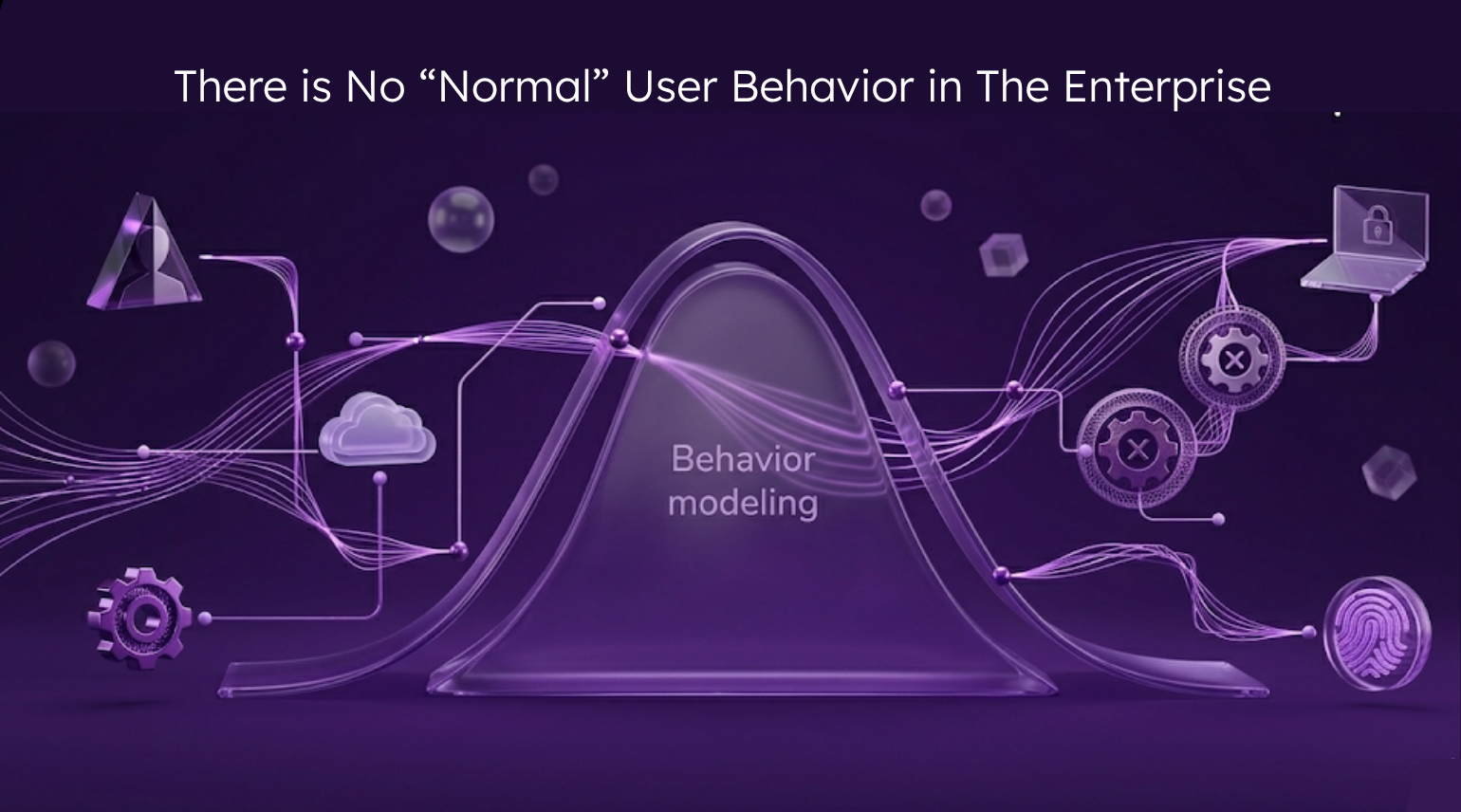
Reveal monitors identity behavior after authentication, flagging rare and risky actions before damage is done – whether the threat is an outsider who slipped in, or an insider employee with the wrong intentions.