After years working in identity security, I can say this pretty confidently:
Many security tools are too granular. They solve very measurable and concise problems, but these problems are all just little slices of a larger, very complex problem identity security practitioners are facing.
Most identity teams I’ve been part of, or worked alongside, were doing the right things. We had controls, policies, and tools… so many tools. But somehow, it still felt harder than it should have been to answer simple questions like: Is this actually risky? Is this normal behavior or something off? Do I need to act right now, or can this wait?
And unfortunately, the reality in answering any of those questions was: “Give me a few hours to pull logs and figure it out.”
Looking back on my experiences, there are a few things I really wish I had.
1. Real Visibility (Not Just More Data)
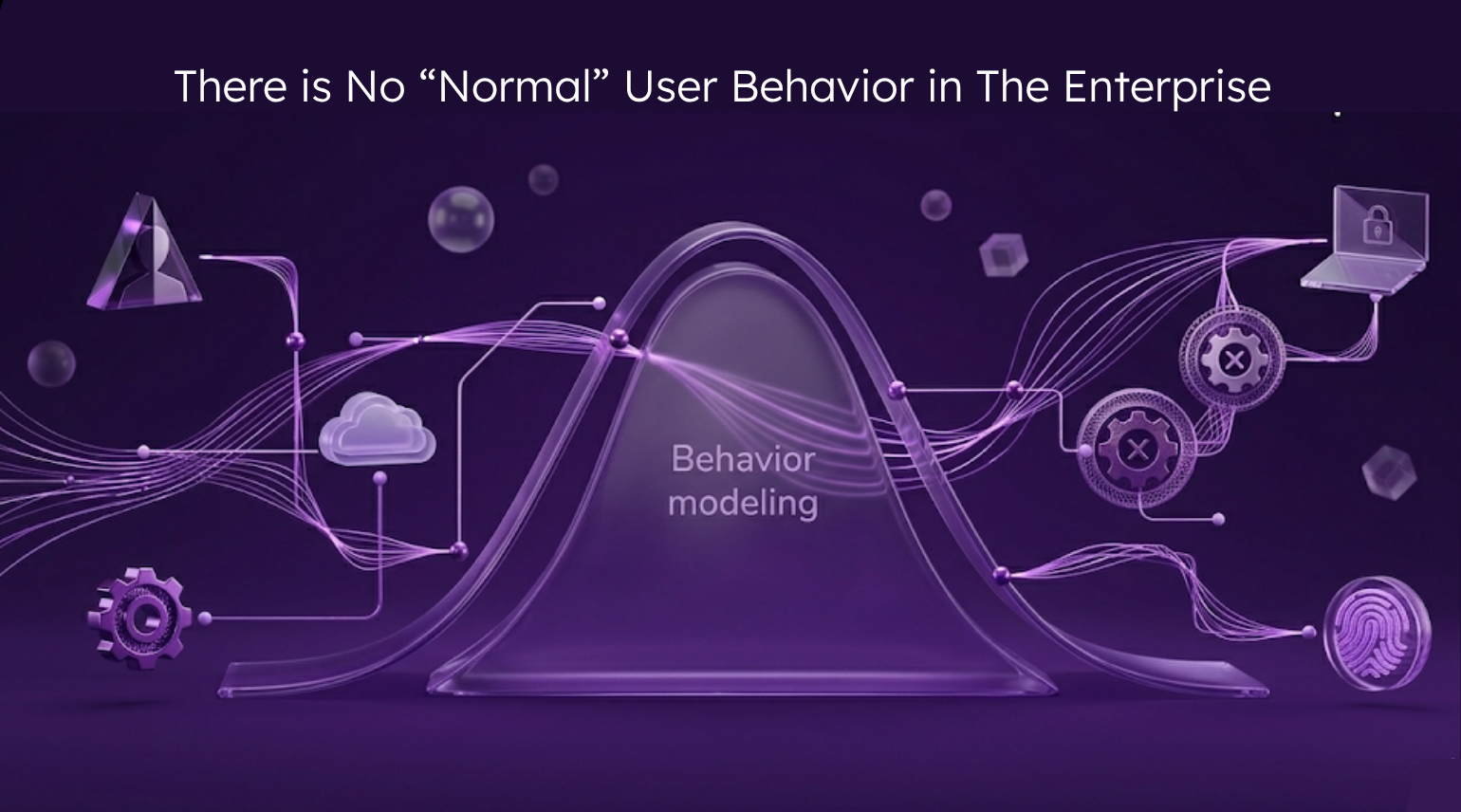
We weren’t lacking data. We were drowning in it. Identity data in one system, access data in another, activity logs somewhere else, and if you were lucky, maybe a spreadsheet tying it all together.
What I actually needed wasn’t more dashboards. It was a single place that correlated all of the data together to build a story. I needed to understand who the identity is, what access they have, what they’re actually doing, and how behavior is changing over time. A true “single pane of glass” is one of those phrases that gets overused by marketing, but when you don’t have it, you feel it every day. Without it, every investigation into anomalous behavior starts from zero and you only get to piece things together fractions at a time.
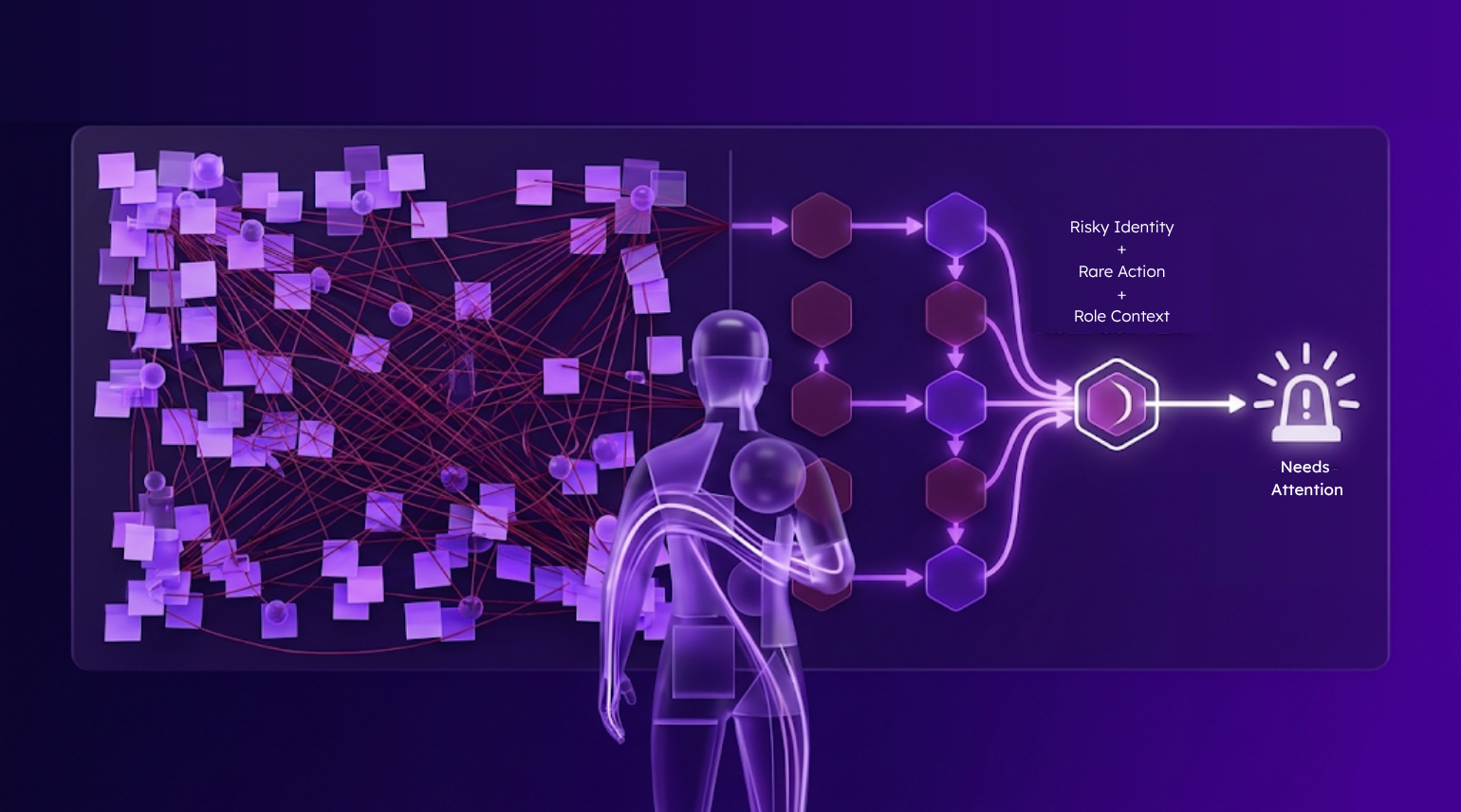
2. Context (Because Rare ≠ Risk)
Just because something is unusual or fires an alert, doesn’t mean it’s dangerous.
Most tools are really good at telling you what’s rare. They are not very good at telling you what’s an actual risk. So you end up chasing things like a developer accessing a system they don’t normally touch, a login at an odd hour, or a spike in activity that turns out to be quarter-end reporting. All technically anomalies. Very often completely legitimate.
What I needed was context. Is this aligned with the user’s role? Has something recently changed? Does this pattern match known good behavior elsewhere? In other words, help me understand why this matters, not just that it’s different.
3. Smarter Policies (That Actually Scale)
Policies always look great until they meet reality.
In theory, they are implementing least privilege, clean roles, and minimal exceptions. In practice, it often looks like “temporary” access that lives forever, service accounts no one wants to touch for fear of breaking things, exceptions layered on exceptions, and business needs that don’t fit neat models. And suddenly, your identity program becomes exception management.
What I wish we had were smarter, adaptive policies. Policies that learn from real usage, policies that can evolve without full manual rewrites, and policies that reduce exception intake instead of creating more.
4. Time (The Most Expensive Resource We Had)
If I had to quantify the biggest hidden cost in identity operations, it would be time spent stitching together the story.
Pull logs. Correlate events. Validate access. Check history. Ping someone on Slack. Wait. Follow up.
Even in mature environments, a “quick” investigation could easily take 30–60 minutes. And that’s when everything goes right. Multiply that across the number of alerts and access reviews the average enterprise gets and suddenly your team is facing an insurmountable mountain of manual correlation.
What I wish I had was faster correlation, pre-built investigation context, and confidence without needing five different tools. Because speed isn’t just efficiency, it’s risk reduction.
Final Thoughts
Identity security isn’t just a control problem, in many ways it’s an operations problem.
The teams that succeed aren’t the ones with the most tools. They’re the ones that can see clearly, understand quickly, and act confidently without burning time on work that shouldn’t exist in the first place.
If you’re in identity today, you’ve probably felt some of this. So it’s worth asking: does this give me real visibility, or just more data? Does it add context, or just flag anomalies? Does it save time, or shift the work somewhere else? Does it reduce exceptions, or create new ones?
Because the goal isn’t a perfect identity program. It’s making better decisions, faster, with more confidence.