This is the third and final part of a series taking a look at the rise of pre-emptive identity security and the need to detect and disrupt adversarial attack activity before it completes. The first article introduced the concept of shifting “left of boom” in identity with the second focused upon application activity analytics. This final article will take a look at how to get started with such a concept.
Understand The Landscape
- Discover Identities, Accounts, Applications & Permissions
- Devise IAM Threat Model
Discovery
It is clearly imperative to discover and have visibility over an asset landscape before any security controls or counter measures can be selected. Whilst this seems a clear and well defined concept in the information security field, identity and access management has not always been managed from that viewpoint. Early employee IAM features were deployed with a productivity or compliance initiative as the main driver, with no compelling event for single pane views of all identity, account and usage activity.
It is first important to identify some key business or team objectives – and how the underlying applications and services support those objectives. Analyse key workflows and business processes. From an identity perspective it is then important to identify where identity is helping or hindering. This aspect we will extend further with respect to things than can potentially be harmful to this identity layer or could do wrong.
Guidance: When identifying high risk applications or high risk events within those applications, work back to identify the entire access path – from identity provider, authentication, session issuance and access enforcement journeys. What stages are involved, what and where are the infrastructure components located?
But understanding the linear inbound (and outbound) identity flows is only one dimension. The second and often more subtly complex aspect is starting to discover the interrelated flows between both accounts and other applications. This is similar to blast-radius style analysis, but the idea is to build an architecture and possible business case for understanding high risk activity across a range of systems.
Guidance: Understanding the relationship between applications and the associated activity helps to build risk models and also identity security architecture principles, including future detection models and response options.
IAM Threat Model
Discovery of assets, applications and potential access paths is the initial phase of any security design. But it is important to extend this thinking into the identity threat model. Whilst threat modelling is a mature concept, specific IAM related threat modelling and assessment can still be quite nascent in some industries. The idea is to help solidify a few basic concepts so that detection models can be fine tuned and response measures applied. Basic threat modelling follows a few simple steps:
- What is being worked on?
- What can go wrong?
- What can we do about it?
- How are we measuring what we did?
If we take this construct and apply specifically to our identity and application activity world we can immediately start the benefits this may bring.
- Identifying threats to identity components (like phishing, credential stuffing, privilege escalation, session interference etc.)
- Mapping attack paths that adversaries might use to exploit identity weaknesses – which should include human and non-human routes – across both data and behaviour
- Understanding the assets at risk, such as access tokens, user credentials, sessions or privileged roles within the application environment and the impact of compromise
- Prioritizing vulnerabilities and planning mitigations using IAM tools and processes
We have started to break down some core identity related activity within an application and in turn what could potentially go wrong. What vulnerabilities may exist and how can those vulnerabilities be exploited?
A real benefit of this is to be able to communicate identity risk effectively to all parts of the business. By identifying core business objectives, linking to application activity, and in turn identifying how identities are accessing these applications allows a tiered model of risk management to be created and also shows the impact of lower level identity threat along with the necessary identity security controls that could be deployed.
Guidance: Think about core applications, activities within them and their access methods – but do so from an identity-centric perspective, understanding relationships and the blast radius of suspicious activity.
Identify High Risk Identity Events
- Pinpoint Events and Applications
- Design Detection and Response Steps
- Know When and How to Respond
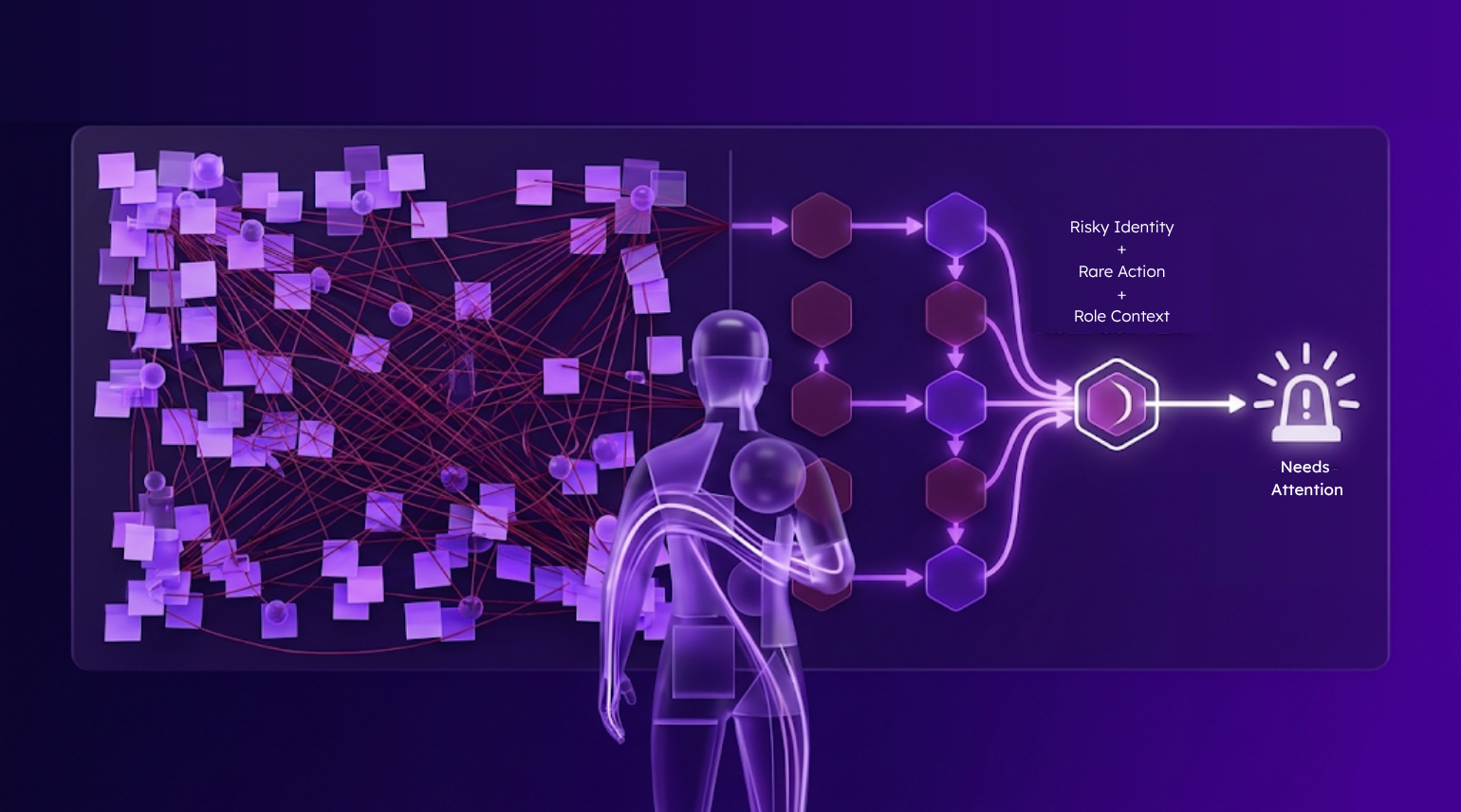
An identity-centric threat modelling approach – either offline and through table top exercises or through threat detection software – helps organisations identify high-risk events and application activity that traditionally would have been hidden in security blind spots. Attack types like account take over, privileged abuse and identity attack surface expansion due to misconfiguration are difficult to identify using a rules-based approach. Rules are static whilst risk is dynamic – especially if that risk is related to the behaviour of malicious actors.
Risk analysis must therefore also be more flexible – taking into account a variety of data sources and not rely on static ways of quantifying likelihood and impact. Composite ways of analysing risk is critical and should be based on defining the “baselines” of usage for both humans and non-humans. This should likely include ways of analysing accounts and personas into peer-like groups, that makes the ability to identify suspicious activity easier. A key consideration though, is not just how to identify high risk events, but how to respond when you do.
This may require different security personnel who are able to operate and manage an identity threat alerting system and process – but more importantly they need to be presented with “human-readable” risk and threat information. Operations teams are rapidly exhausting their finite resources to triage alerts. Vulnerability, exploitation and risk information needs to be presented in ways that can elevate the ability of an operator to quickly approve any presented remediation recommendations.
These remediation stages are likely to be “high fidelity” – with subtle changes to runtime access, session and authorization steps – and not just a coarse grained logout or disabling of an account.
Whilst the security metrics involved (mean time to detect and mean time to respond) should be leveraged, the main concept behind a pre-emptive security model is to not only identify an attack inflight – but also respond successfully before it completes. This response action should also include changes to existing security controls and policy – in order to prevent future attacks using similar patterns.
In order to do so, it is important to have cross-organisational agreement on how policy can and should be changed – which will involve both business and technical stakeholders. Changes to security controls such as MFA adoption or authorization policy based access control should be supported by clear metrics that can be communicated to different parties.
Guidance: Identify and understand the operating model around identity threat – from alerting format, triage and how remediation stages will be approved and fulfilled across a range of identity system components and ticketing and alerting systems.
Onboard, Analyse and Prevent
- Leverage API-first onboarding
- Describe Normal
- Prepare for the Abnormal
Some practical steps should also be considered with respect to getting started on a pre-emptive journey. High-fidelity alerting requires data. This should be ingested from a range of sources – from core business applications and infrastructure, but also the core identity components too – from authentication, access enforcement and security logging platforms. Clearly this should be a configuration task not a customization one and be done in a way that is read-only or non-disruptive to running systems and processes. This normalized data-lake becomes the bedrock of future identity-threat modeling and response.
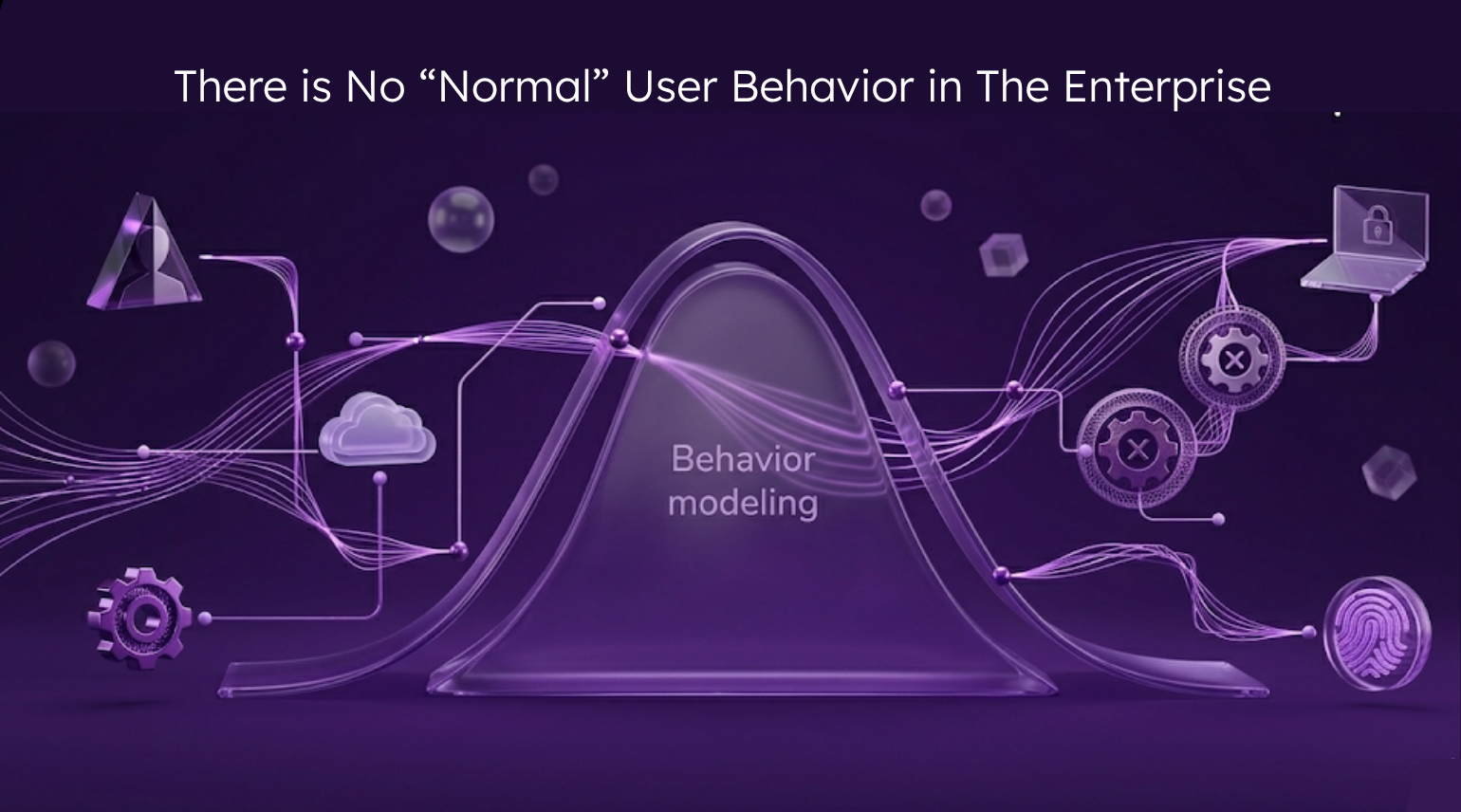
With data becomes the ability to describe “normal” – normal authentication, normal authorization, and normal activity. This needs to be done for all entities within an application – covering both people and non-human identity.
The strategic aspect that is emerging, however, is the ability to analyse activity – the post-authentication events that can help to support identity intent. The correct identity has passed a biometric authentication, assigned the correct permissions and passed a policy enforcement point – but intent – be it malicious or benign – is becoming the critical battleground for stopping complex attacks. A difficult and pressing extension to this, is how to analyse activity and intent for agentic-AI.
Agentic-AI is, by design, built for optimization. Constant improvement of the given task is essential to improve results, learn and reduce any latency or discrepancy. This in turn creates challenges with respect to permissions assignment and also behavior baselining.
Agentic, for example, may well continue to accumulate permissions and see considerable variance in application behaviour – some of which may well be legitimate, until a more stable pattern of usage occurs. A service API that is used to create DNS records for example may well be more deterministic – with stable volume, time of day, request and response payloads.
Organisations must evolve to be in a position to “prepare for the abnormal”. This will require potential changes to risk identification as discussed, as well as operating teams and how best to respond.
Pre-emptive identity security is about “spying the lie”. Whilst this can often be simpler in the physical world, within a digital setting this is becoming increasingly more complex. Attribution of threat actors and their intent requires a broad data lens and strong composite risk analysis model. The result however is that organisations position themselves to stop serious identity fraud and data theft before it happens.
Learn more about the Reveal Preemptive Identity Security platform here.